Device Intelligence: A Core Layer in Modern Fraud and Risk Management
Device intelligence is the analysis of technical and behavioral signals from a user’s device to assess fraud risk, credit risk, and session integrity in real time without relying on PII (Personally Identifiable Information). As financial services become increasingly digital and hybrid, traditional trust signals are becoming less reliable. Credentials can be stolen, identities fabricated, and personal data replayed at scale.
In this environment, device intelligence is increasingly used to strengthen fraud prevention, credit risk assessment, authentication, and digital decisioning. Rather than relying only on declared identity or static user attributes, it evaluates whether the digital environment behind an interaction appears coherent, stable, and trustworthy.
This article explains what device intelligence is, how it differs from device fingerprinting, how it works, and why it has become an important part of risk management strategies for banks, fintech companies, BNPL providers, and digital lenders operating at scale.
Device Intelligence is the analysis of technical and behavioral signals from a user’s device to assess risk in real time, without relying on PII (Personally Identifiable Information). It typically operates alongside fraud detection, risk monitoring, and credit decisioning systems as an additional analytical layer. Rather than replacing these systems, device intelligence strengthens them by providing an independent stream of behavioral and technical signals.
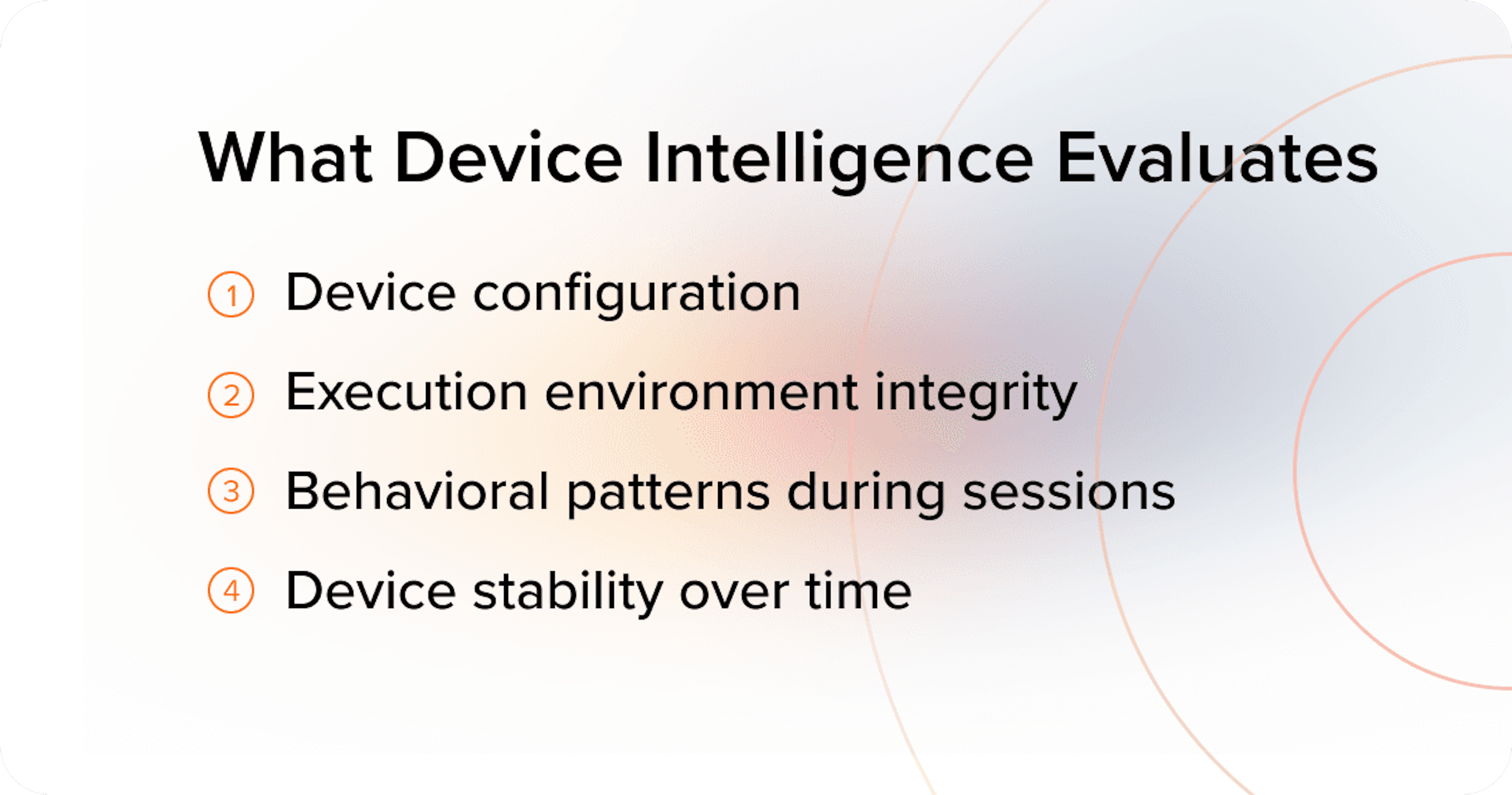
It evaluates:
Unlike identity verification or authentication, device intelligence is not primarily designed to prove a user’s identity. Instead, it evaluates whether the digital environment behind an interaction appears consistent and trustworthy.
Fraud has shifted away from isolated attacks toward systematic manipulation of digital environments. Organized fraud rings increasingly operate as coordinated infrastructure – combining stolen identities, controlled devices, automation, and distributed financial accounts. Investigations across multiple regions illustrate this trend. In Southeast Asia, large-scale scam compounds operating in Cambodia and Myanmar have evolved into an industrial cyber-fraud sector generating tens of billions of dollars annually and employing hundreds of thousands of operators targeting victims worldwide.
At the same time, law-enforcement operations in India regularly uncover fraud networks built around mule bank accounts, SIM card pools, and coordinated digital onboarding infrastructure used to route illicit transactions and conduct large-scale scams.
Meanwhile, in Latin America, organized cybercrime groups have developed sophisticated banking malware operations. Brazilian threat groups behind the Grandoreiro banking trojan have run large-scale campaigns targeting financial institutions across multiple countries, enabling attackers to execute fraudulent banking transactions by manipulating infected devices and sessions.
Instead of breaching systems directly, attackers increasingly exploit weaknesses in how platforms recognize and trust devices.
Common tactics include:
Depending on the detection capabilities of the platform, these techniques can allow fraudsters to appear as “new” users repeatedly, gradually degrading fraud controls and credit models over time.
Device intelligence links risk signals to device behavior patterns and can help detect:
– even when identities, credentials, or declared attributes look valid.
Explore in more detail:
→ How Device Intelligence Prevents Fraud in Real Time
→ First-Party Fraud: The Hidden Threat Draining Your Business of Profits
→ Third-Party Fraud: Types, Examples, Prevention Methods
Device fingerprinting focuses on identifying a device, while device intelligence evaluates whether the environment behind it can be trusted.
Device intelligence analyzes combinations of technical signals such as browser configuration, operating system parameters, hardware characteristics, and other observable attributes. Modern fingerprinting methods may also incorporate dynamic or behavioral elements.
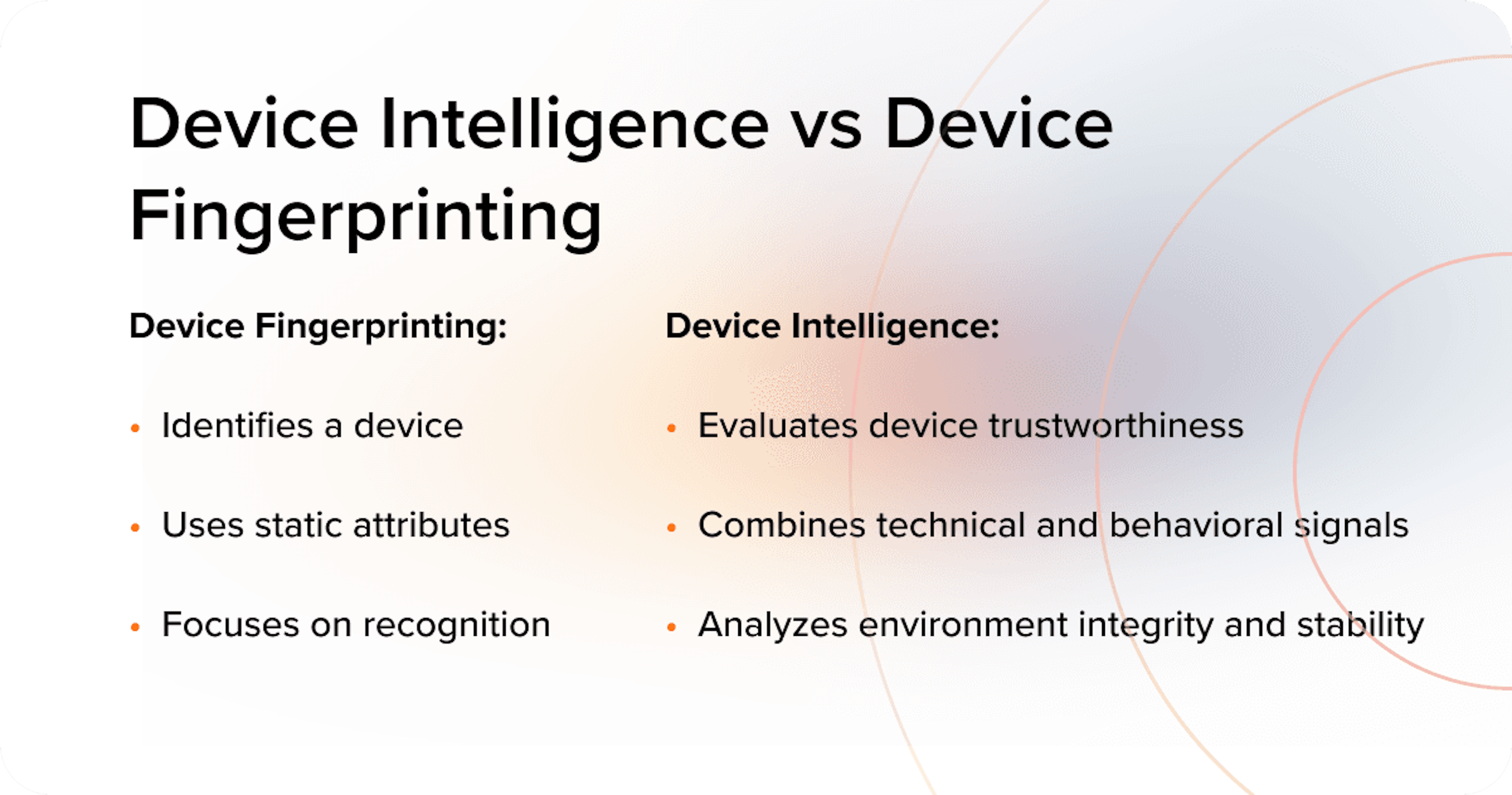
While effective for device recognition, fingerprinting primarily answers the question of device identity. Its reliability can be affected by privacy controls, fingerprint randomization, spoofing tools, and increasingly complex execution environments.
Device intelligence builds on this foundation by evaluating the integrity and consistency of the environment in which the device operates. It can incorporate:
Explore in more detail:
→ Introduction to Device Fingerprinting
→ Browser Fingerprinting: What It Is & How to Mitigate Risk
Modern fraud and risk management rely on multiple layers of analysis, each addressing different aspects of a digital interaction. Device intelligence occupies a critical position within this architecture, sitting between identity verification and behavioral monitoring.
Identity-based controls such as KYC, document verification, and authentication mechanisms confirm who the user claims to be. Transaction monitoring evaluates what the user does during financial activity. Device intelligence focuses on the environment through which the interaction occurs – analyzing device configuration, execution integrity, infrastructure conditions, and behavioral patterns associated with the session.
This layer provides early risk context before transactions occur and continues to supply signals throughout the session lifecycle. When combined with behavioral analytics and transaction monitoring, device intelligence helps risk teams distinguish legitimate users from manipulated or automated environments, even when credentials and identity attributes appear valid.
In practice, device intelligence can be implemented in several ways. Some organizations rely on external technology providers, while others build internal device analytics capabilities within their own infrastructure. Increasingly, institutions combine both approaches.
The choice typically depends on factors such as the organization’s technical maturity, data science resources, time-to-market requirements, and the complexity of the products being protected.
Vendor-based device intelligence is typically delivered by specialized providers through SDK integrations, APIs, or SaaS solutions.
Such solutions usually provide:
At the same time, organizations using external solutions typically have less direct control over the underlying logic of signal processing and model development.
This approach is common among fintech companies, BNPL providers, microfinance organizations, and banks that prefer to rely on specialized expertise rather than build large in-house data science teams.
Many providers – including JuicyScore – combine global fraud intelligence with the ability to customize models and signals for specific clients. By analyzing device behavior and fraud scenarios across multiple countries and industries, such providers continuously identify new attack patterns and adapt their detection logic while tailoring models to each organization’s risk environment.
Some institutions develop internal device analytics systems as part of their own risk infrastructure.
These systems are typically:
Internal device intelligence allows organizations to maintain full control over model design, data processing, and risk decision logic.
However, building such systems requires significant investment in data infrastructure, engineering capabilities, and specialized data science teams. Development cycles are typically longer, and internally built models may initially lack broader visibility into fraud patterns observed across the wider market.
In practice, many organizations adopt a hybrid architecture that combines external device intelligence providers with internal analytics capabilities.
In this model, external solutions supply large-scale signal collection, cross-market reputation data, and visibility into emerging fraud patterns observed across multiple clients and geographies. Internal teams then build additional analytics, rules, and models on top of these signals using their own historical data and product knowledge.
Hybrid architectures allow institutions to:
This layered approach is increasingly common among mature fintech companies and banks with established risk teams. External providers contribute broad market visibility, while internal analytics teams focus on product-level optimization and decision-making logic.
Modern fraud operates across multiple layers – identity, device, network, and transaction flows. The device and session environment, however, often become the execution layer where manipulation occurs and where many fraud signals first appear.
Attackers manipulate device attributes to evade recognition and reputation systems.
→ Device Spoofing as a Structural Risk in Digital Lending
Software environments can be used to simulate thousands of “clean” devices at scale.
→ Virtual Machine Detection: The Overlooked Risk Factor in Digital Lending
→ JuicyScore’s research: Risks of Virtual Machines and the Best Ways to Detect Them
Many application fraud schemes rely on automated or manipulated environments rather than stolen identities.
→ Application Fraud: Detection and Prevention Methods
The same underlying device reused across multiple identities, applications, or accounts.
Effective device intelligence evaluates three dimensions continuously.
Real devices follow physical and software constraints. Inconsistencies often indicate manipulation. Device intelligence systems therefore analyze a large number of parameters describing the device, its environment, and the way it is used during a session. In the JuicyScore solution, more than 65,000 events – or device-related data points – may be collected during a single online session, with most of them aggregated into datasets describing the device environment and its behavior.
Legitimate devices evolve gradually. Frequent resets, re-randomization, or sudden changes in device characteristics may indicate elevated risk.
Human-operated devices exhibit natural variation. Automated environments do not. Device intelligence models often aggregate signals across multiple dimensions of behavioral interaction patterns, infrastructure conditions, and device quality.
These behavioral signals – such as navigation rhythm, interaction timing, and application patterns – can reveal risk markers that are invisible in traditional identity-based data.
Risk emerges from patterns across layers, not single anomalies – a principle explored in:
→ Device Intelligence as a System-Level Risk Layer: From Signals to Structured Risk Context
→ The True Value of Users’ Online Behavior Data
→ Rare Events Risk Assessment: How Data Science Can Help Business Thrive
Device intelligence platforms analyze signals across multiple layers of the digital environment.
Device Configuration Signals:
Environment Integrity Signals:
Behavioral Signals:
Longitudinal Signals:
Device intelligence delivers the strongest results when combined with behavioral analytics.
Behavioral signals include:
This combination is especially effective against scripted abuse and bot-driven fraud.
Explore in more detail:
→ Seeing Clearly Online: How New Digital Signals Help Models Manage Risk More Effectively
→ An Introduction to Behavioral Biometrics
→ Comprehensive Guide to Bot Mitigation
Detecting account takeover attempts despite valid credentials
→ What Is Account Takeover (ATO) and How to Prevent It
Helping to identify synthetic and AI-driven fraud environments
→ What Is Synthetic Identity Fraud and Why It’s Growing
→ Generative AI–Driven Fraud: Detection, Prevention, and the Future of Risk Management
Supporting alternative credit scoring in thin-file environments
→ What Is Alternative Credit Scoring and Why It Matters
→ Device Intelligence in Credit Scoring: How to Assess Risk Without Personal Data
Protecting model quality from device-level noise
→ Microfinance Fraud Detection: Protecting Digital Lenders from External Threats
Enabling inclusion in high-growth markets
→ Banking the Next 30 Million: Why Device Intelligence Is Key to Financial Inclusion in Indonesia
→ Device Intelligence: Building Trust in India’s Digital Lending
Case Studies
→ Risk Control Without Heavy Lifting: PitaCash Use Case in SEA
→ Credito 365 Cuts Risk on Repeats and Prevents Fraud with JuicyScore
→ How ATM Online Boosted Risk Models and Cut Fraud in Vietnam with JuicyScore
→ MoneyMan MX leverages JuicyScore to increase approval rate x 1.5 times
Device intelligence helps detect device switching, session abuse, and repeated transaction-level manipulation.
→ Detecting Payment Fraud with Machine Learning
→ Payment Screening for Preventing Transaction Fraud
Device intelligence complements, but does not replace, payment-specific controls.
Modern device intelligence relies on non-personal technical and behavioral signals, rather than PII.
This design supports compliance while preserving risk visibility – a balance explored in:
→ Security vs Privacy: In Search of a Fair Balance
Recent regulatory context further reinforces this shift. India provides a clear example:
→ PII-Free Risk Scoring: Why Device Intelligence Fits India’s DPDP Era
→ Practical Guide to India’s Final DPDPA Rules
→ RBI’s 2025 Authentication Mandate: Why Device-Level Intelligence Is Now Critical
For enterprise risk teams, device intelligence is not a feature. It is infrastructure.
It underpins:
Organizations that embed device intelligence early may gain resilience without increasing friction. Those that delay often compensate later with stricter rules, lower approval rates, and degraded user experience.
→ Introduction to Device Fingerprinting
→ The Future of Device ID in the Digital World
→ Device Spoofing as a Structural Risk in Digital Lending
→ Virtual Machine Detection: The Overlooked Risk Factor in Digital Lending
→ Seeing Clearly Online: How New Digital Signals Help Models Manage Risk Effectively
→ The True Value of Users’ Online Behavior Data
→ Device Intelligence as a System-Level Risk Layer: From Signals to Structured Risk Context
→ How Device Intelligence Prevents Fraud in Real Time
→ Microfinance Fraud Detection: Protecting Digital Lenders from External Threats
Device intelligence is the analysis of technical and behavioral signals from a user’s device to assess risk in real time, without relying on personal data. It evaluates whether the digital environment behind an interaction is coherent, stable, and consistent with legitimate human use.
Device fingerprinting relies on static attributes such as browser version or screen resolution to recognize devices. Device intelligence goes further by analyzing environmental integrity, behavioral consistency, and stability over time. Fingerprinting answers whether a device looks familiar; device intelligence determines whether the environment itself can be trusted.
Yes. Many modern fraud attacks operate with valid credentials, OTPs, or session tokens but originate from manipulated, automated, or virtualized environments. Device intelligence detects these inconsistencies at the device and session level, even when identity-based checks pass.
Device intelligence adds contextual, non-PII signals to credit decisioning, helping risk models distinguish between genuine and manipulated environments. This is especially valuable in thin-file, no-bureau, and emerging-market contexts, where traditional credit data is limited or unreliable.
Device intelligence relies on non-personal technical and behavioral signals and does not directly identify individuals. When designed with privacy safeguards and data-minimization principles, these approaches can operate in alignment with regulatory frameworks such as GDPR in Europe, LGPD in Brazil, and India’s DPDP, while still providing meaningful risk visibility at scale.
No. Device intelligence does not replace authentication controls. It complements them by providing continuous, session-level risk context before, during, and after authentication, while MFA and OTPs verify access at a specific point in time.
Device intelligence helps detect and prevent a wide range of fraud patterns, including:
Its strength lies in identifying environmental manipulation rather than relying solely on identity signals.
In emerging markets, devices are often shared, infrastructure conditions vary, and credit histories are fragmented. Traditional identity- and document-based controls perform poorly in these environments. Device intelligence adapts by focusing on environmental consistency and behavior instead of formal identity attributes.
Device intelligence becomes critical when:
At scale, device intelligence functions best as core risk infrastructure, not a bolt-on control.
Explore how device intelligence improves fraud detection, credit scoring, and onboarding – with real-time analysis and privacy-first design.
Device spoofing quietly weakens fraud prevention and credit models. Learn how spoofed devices work and how lenders can detect them with device intelligence.
When personal data stops explaining credit risk, scoring needs a new lens. How device intelligence restores visibility in digital lending.
Get a live session with our specialist who will show how your business can detect fraud attempts in real time.
Learn how unique device fingerprints help you link returning users and separate real customers from fraudsters.
Get insights into the main fraud tactics targeting your market — and see how to block them.
Phone:+971 50 371 9151
Email:sales@juicyscore.ai
Our dedicated experts will reach out to you promptly