Account Takeover Prevention with JuicyScore
Protect your users from unauthorized access, detect session anomalies, and stop account takeovers before damage is done. JuicyScore uses device intelligence and behavioral analytics to help digital platforms identify suspicious logins and secure high-risk sessions — without collecting personal data.
Book a Demo
Leaders Grow with JuicyScore








Spot the Signs Before They Log In
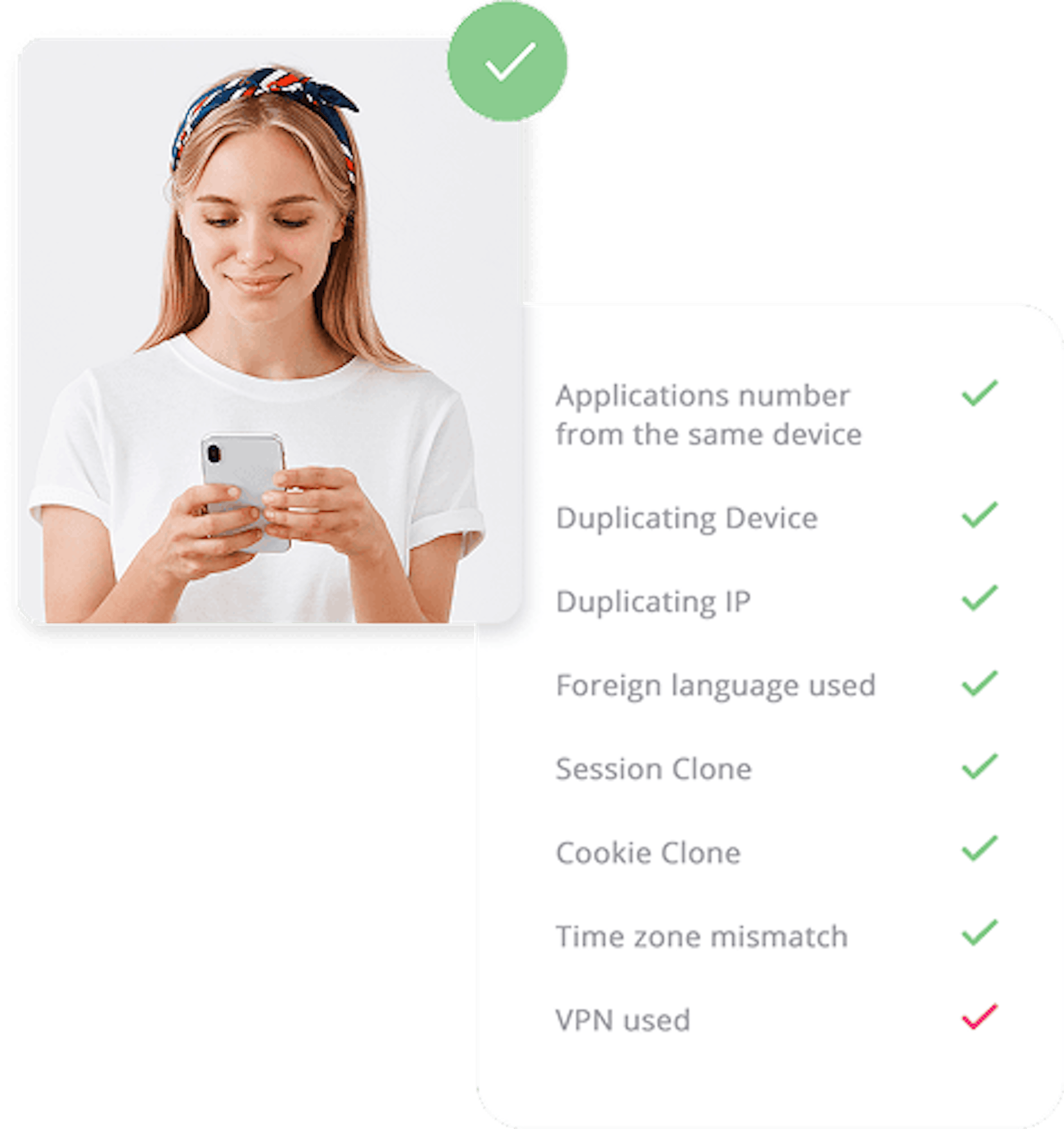
Account takeover attacks often rely on stolen credentials, device spoofing, or session replay tools. Traditional authentication checks don’t detect this level of manipulation. JuicyScore continuously analyzes login behavior, device consistency, and network anomalies to stop unauthorized access — even before the password is entered.
Real-Time Protection for Trusted Users
Detect IP inconsistencies, device emulation, and proxy use
Block access from unusual locations, anomalous time zones, and rotating devices
Identify risk signals during session start or login
Prevent session hijacking without adding friction
Reduce fraud losses and maintain user trust

Learn How It Works
Utilizing over 65,000 data points, JuicyScore generates highly predictive risk score models to detect fraud and assess risk in real time. Our output data vector includes device intelligence, user behavioral patterns, internet connection insights, and software data for precise decision-making. Protect your business with advanced fraud prevention while ensuring a seamless customer experience.
Learn more
Our Clients’ Success Stories
Related Articles
Discover Other Products
See How We Spot Fraud Before It Happens — Book Your Expert Session
See It in Action with a Real Expert
Get a live session with our specialist who will show how your business can detect fraud attempts in real time.
Explore Real Device Insights in Action
Learn how unique device fingerprints help you link returning users and separate real customers from fraudsters.
Understand Common Fraud Scenarios
Get insights into the main fraud tactics targeting your market — and see how to block them.
Our Contacts:
Phone:+971 50 371 9151
Email:sales@juicyscore.ai
Leading Brands Trust JuicyScore:
Get in touch with us
Our dedicated experts will reach out to you promptly