Transaction Fraud: Detection, Prevention, and How It Actually Works


Most fraudulent activity does not begin with a clearly suspicious transaction. It begins with something that looks entirely normal – a login, a balance check, a small payment. Only later, when viewed in sequence, does it become clear that these actions were part of a coordinated attempt to extract value.
For risk teams, this creates a structural challenge. The problem is not identifying obvious fraud, but recognizing when legitimate-looking activity becomes fraudulent.
Fraud transaction is defined as any financial or digital transaction executed with deceptive intent to gain unauthorized value, access, or advantage. This includes card fraud, account takeover, synthetic identities, and coordinated abuse across multiple accounts.
This definition shifts the focus from isolated transactions to connected behavior. A fraud transaction is rarely a standalone anomaly. It is typically one step within a broader pattern that unfolds across sessions, devices, and time.
Transaction fraud is often described in terms of individual actions, but in practice it behaves more like a sequence.
A payment may follow a valid login. A loan may be issued to a real device. A user journey may appear consistent at every step. The issue only becomes visible when these actions are connected and interpreted together.
In practice, transaction fraud often appears through patterns such as:
For example, a borrower may pass onboarding checks and receive approval, but submit multiple applications across accounts from slightly varied environments. Without device continuity, these appear unrelated. With environment-level analysis, they form a coordinated pattern.
Account takeover makes this pattern explicit. A fraudster gains access using legitimate credentials and behaves in a way that mirrors the original user. The resulting transaction appears authenticated and technically valid.
A similar pattern appears in online fraud transactions driven by automation. Instead of one large suspicious action, fraudsters generate multiple smaller interactions designed to stay below detection thresholds. The signal is not in the transaction itself, but in repetition, timing, and structure.
Fraud transaction detection is not limited by signal availability – it is limited by how signals are connected and interpreted.
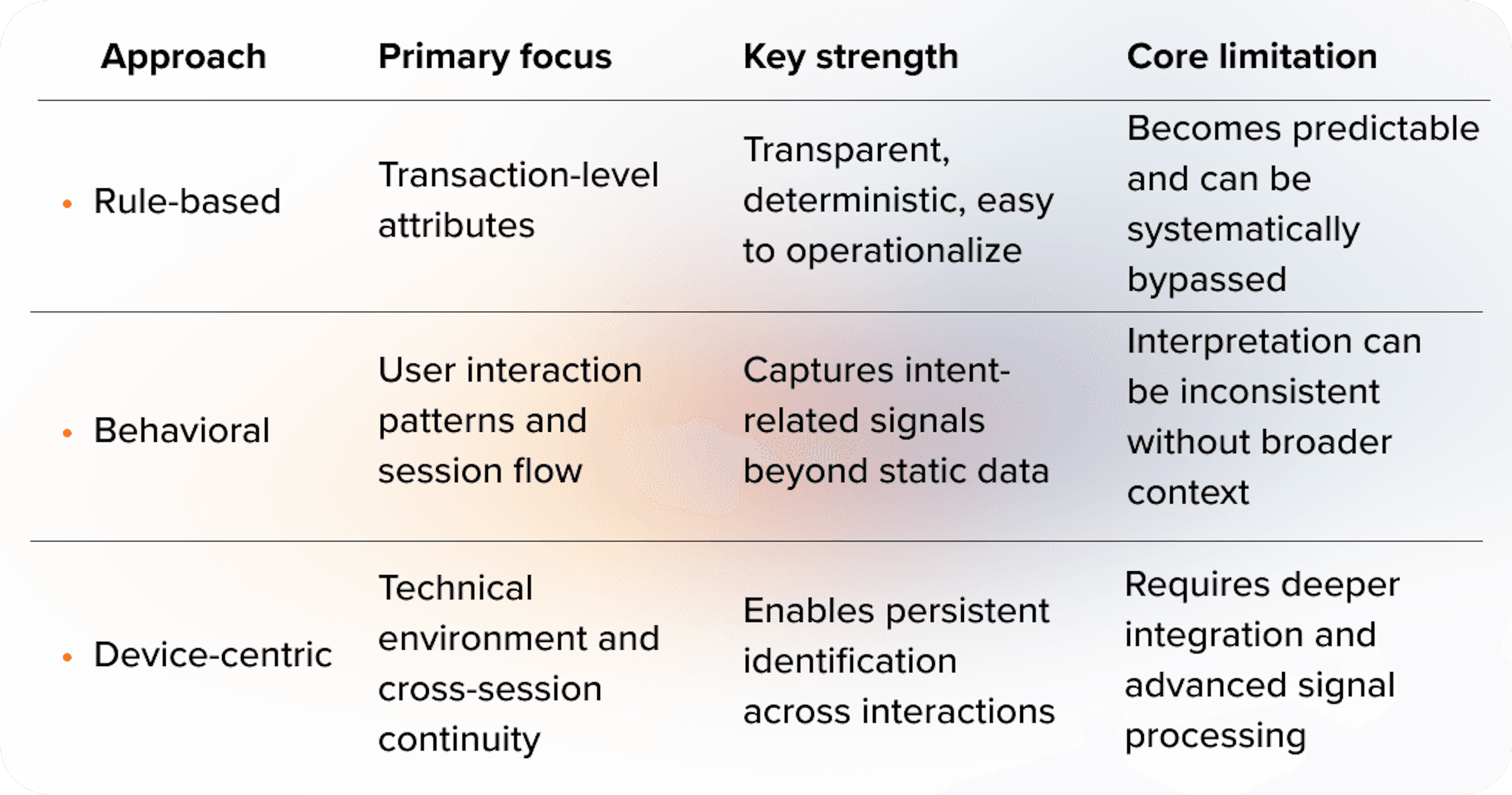
Rule-based systems remain the foundation in many organizations. They define what is considered abnormal and trigger alerts when thresholds are exceeded. This approach is easy to implement and explain, but it becomes predictable over time.
Behavioral analysis adds another layer by focusing on how users interact with a system. It captures patterns such as navigation flow, timing, and consistency. This helps identify intent, but without additional context, behavior alone can be difficult to interpret.
Device intelligence introduces persistence. It evaluates the technical environment behind each interaction and connects activity across sessions. This exposes patterns that are invisible at the transaction level.
The difference between these approaches is structural. Rule-based detection reacts to predefined conditions. Behavioral analysis interprets actions. Device intelligence connects events across time and environments.
In practice, effective transaction fraud detection comes from combining these layers into a unified, contextual risk assessment.
Understanding how detection methods differ helps clarify why many systems fail to catch modern fraud.
Fraudulent transactions are difficult to detect because they increasingly rely on legitimate signals. The challenge typically comes from a combination of factors:
Authentication validates access, not intent.
But it is often treated as a confirmation of safety. In account takeover scenarios, this assumption breaks down completely.
Another challenge is fragmentation. Fraud does not occur in a single step. It is distributed across multiple actions, each of which may appear harmless. Without connecting these actions, the underlying pattern remains invisible.
A transaction may be approved because each individual signal appears low-risk, while the combination of signals would indicate coordinated fraud if evaluated together.
Automation adds further complexity. Fraudsters use tools that replicate human behavior and operate at scale. Online fraud transactions can be executed in volumes that overwhelm traditional detection systems.
Thin-file borrowers introduce a different type of uncertainty. With limited historical data, it becomes harder to distinguish between genuine new users and high-risk behavior. This is where alternative signals become essential.
Fraud transaction monitoring is defined as the continuous evaluation of transactions, user behavior, and device context to detect and prevent fraudulent activity in real time.
Unlike static detection, monitoring is not limited to a single moment. It operates across the entire session and updates risk as new signals appear.
A session may begin as low-risk and gradually become suspicious as patterns emerge. This allows risk teams to act before loss occurs, not after. Fraud often becomes detectable only after the transaction decision point. Effective monitoring shifts detection earlier in the session.
Real-time monitoring moves fraud detection from post-event analysis to in-session decisioning.
Even well-designed systems have blind spots.
Rule-based systems become less effective as fraudsters adapt to known thresholds. Behavioral models can be misled when fraudulent activity successfully mimics normal behavior. Fragmented data prevents teams from seeing connections between events.
Without environment-level visibility, coordinated fraud across accounts or sessions remains undetected.
These are not isolated failures – they reflect how most systems are designed. Most systems evaluate transactions, while fraud operates across sessions.
Fraudulent transactions are often assumed to be obvious, but most are designed to blend in. They look legitimate because they are built on legitimate signals.
Many detection systems still rely on identifying outliers, while most fraud stays within expected ranges.
Another misconception is that more data automatically improves detection. In reality, unstructured data increases noise and reduces clarity.
There is also a tendency to treat fraud as a point-in-time problem. This leads to delayed decisions and fragmented controls.
For banks, fintech companies, and digital lenders, improving transaction fraud detection requires a shift in how risk is evaluated.
Transactions need to be assessed in context, not in isolation. Signals should be connected across sessions, devices, and time. Risk evaluation should happen continuously rather than at a single checkpoint.
Missed fraud leads to direct financial loss. Excessively strict controls reduce approval rates. Fragmented detection increases manual review costs.
A user may pass onboarding and authentication, but operate from an inconsistent device environment during a transaction. Without device-level analysis, this change remains invisible.
This is particularly important when working with thin-file borrowers, where traditional data is limited and uncertainty is higher.
Device intelligence is not another signal layer. It is the layer that connects sessions, environments, and identities into a continuous risk view.
JuicyScore supports this approach through a device intelligence risk scoring solution that enables contextual fraud detection without relying on personal data. By combining technical and behavioral signals, it helps risk teams improve model accuracy while maintaining approval rates.
Book a demo with JuicyScore to see how device intelligence improves fraud transaction detection and supports better risk decisions.
A fraud transaction is a financial or digital transaction carried out with deceptive intent to gain unauthorized value or access. It often involves compromised accounts, stolen payment data, or coordinated fraud activity.
Transaction fraud detection combines rule-based checks, behavioral analysis, and device intelligence to evaluate risk. Modern systems assess transactions in context and in real time rather than as isolated events.
Examples include unauthorized card payments, transactions following account takeover, automated bot-driven purchases, and repeated low-value actions designed to avoid detection.
Fraud transaction monitoring is the continuous evaluation of transactions and related signals during a session to detect and prevent fraud before losses occur.
Online fraud transactions often use legitimate credentials and replicate normal user behavior. Fraudsters also use automation tools, making detection difficult without contextual and device-level analysis.
Card fraud is a subset of transaction fraud. Transaction fraud includes a broader range of activities such as account takeover, loan fraud, and digital service abuse.
Fintech companies can improve detection by combining behavioral and device signals, implementing real-time monitoring, and using contextual risk scoring instead of relying only on static rules.

Explore five common types of bank account fraud – from synthetic identities to mule networks – and how behavioral and device-based insights enable earlier, privacy-safe detection.
From deepfakes to AI-generated identities, generative AI fraud is transforming risk. Explore proven strategies to detect and prevent the next wave of digital deception.

What is payment fraud? Learn the main types, tactics, and prevention strategies in 2026. Guide for banks, fintechs, BNPL, and digital lenders.
Get a live session with our specialist who will show how your business can detect fraud attempts in real time.
Learn how unique device fingerprints help you link returning users and separate real customers from fraudsters.
Get insights into the main fraud tactics targeting your market — and see how to block them.
Phone:+971 50 371 9151
Email:sales@juicyscore.ai
Our dedicated experts will reach out to you promptly